Are the posted questions getting worse?
-
May 23, 2019 at 7:25 pm
It seems fitting that Entity Framework would be described as modifying databases that way 🙂
-
May 23, 2019 at 7:45 pm
Wow. Just Wow.
Michael L John
If you assassinate a DBA, would you pull a trigger?
To properly post on a forum:
http://www.sqlservercentral.com/articles/61537/ -
May 23, 2019 at 7:49 pm
Robert Sterbal wrote:Luis Cazares wrote:"They" as Georgia Tech people.
I understand. But who did the injection, and who was tasked with preventing it? Was it an internal or external resource? The details regarding security are as important as the irony.
They haven't released the details. It's only known that it was a web application vulnerability happening since last December and it's now patched.
-
May 24, 2019 at 12:14 am
Michael L John wrote:Wow. Just Wow. https://www.sqlservercentral.com/forums/topic/query-containing-while-loop-for-dates-taking-increditbly-long#post-3646645
I guess that's the word for it. They need some paid help especially in the area of some training.
--Jeff Moden
RBAR is pronounced "ree-bar" and is a "Modenism" for Row-By-Agonizing-Row.
First step towards the paradigm shift of writing Set Based code:
________Stop thinking about what you want to do to a ROW... think, instead, of what you want to do to a COLUMN.Change is inevitable... Change for the better is not.
Helpful Links:
How to post code problems
How to Post Performance Problems
Create a Tally Function (fnTally) -
May 24, 2019 at 1:04 pm
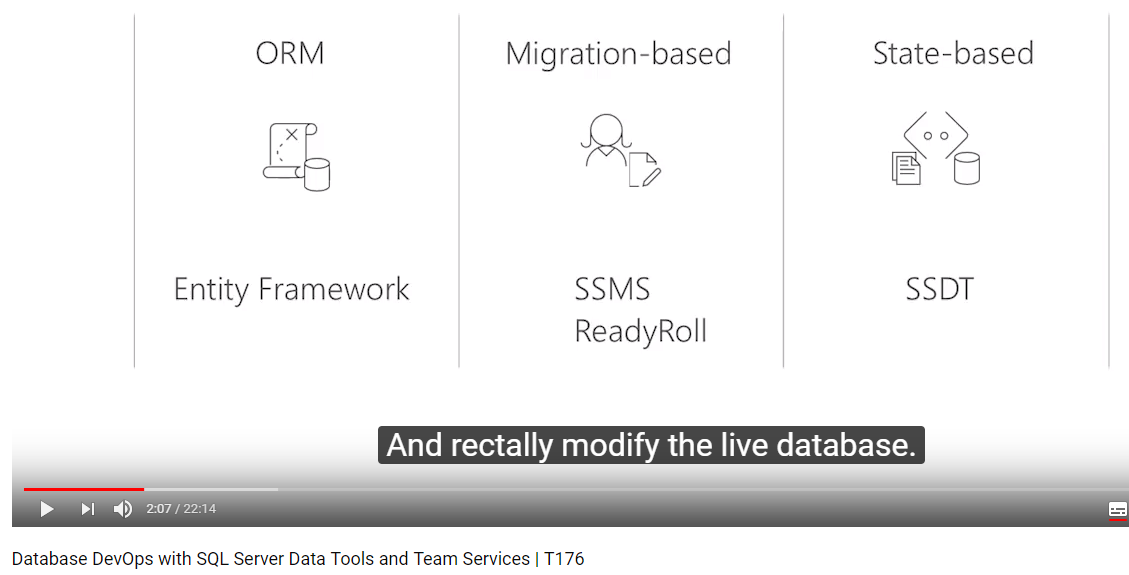
Phil Parkin wrote:I started watching a YouTube video on Azure DevOps. I can't have the sound turned up where I am, so I turned on subtitles. This is as far as I got before I needed to take a guffaw break. I've worked with plenty of databases which deserved this treatment.

Yeah, this is the ugly truth behind DevOps.
"The credit belongs to the man who is actually in the arena, whose face is marred by dust and sweat and blood"
- Theodore RooseveltAuthor of:
SQL Server Execution Plans
SQL Server Query Performance Tuning -
May 24, 2019 at 1:08 pm
I just presented a new session on SQL Injection at Techorama in Belgium and before that at SQLDay in Poland. As part of the prep, I did searches on recent breaches caused by Injection. There are so many. It's completely disheartening. The Georgia Tech one was bad. A worse one was iDressUp, a kids site. It's just nuts that we're dealing with this crap after 21 years of knowing how to fix it.
"The credit belongs to the man who is actually in the arena, whose face is marred by dust and sweat and blood"
- Theodore RooseveltAuthor of:
SQL Server Execution Plans
SQL Server Query Performance Tuning -
May 24, 2019 at 1:35 pm
Grant Fritchey wrote:I just presented a new session on SQL Injection at Techorama in Belgium and before that at SQLDay in Poland. As part of the prep, I did searches on recent breaches caused by Injection. There are so many. It's completely disheartening. The Georgia Tech one was bad. A worse one was iDressUp, a kids site. It's just nuts that we're dealing with this crap after 21 years of knowing how to fix it.
Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing."
The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is.
It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
-
May 24, 2019 at 2:09 pm
Ed Wagner wrote:Grant Fritchey wrote:I just presented a new session on SQL Injection at Techorama in Belgium and before that at SQLDay in Poland. As part of the prep, I did searches on recent breaches caused by Injection. There are so many. It's completely disheartening. The Georgia Tech one was bad. A worse one was iDressUp, a kids site. It's just nuts that we're dealing with this crap after 21 years of knowing how to fix it.
Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing." The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is. It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
Your research would make a great detailed blog post.
412-977-3526 call/text
-
May 24, 2019 at 2:14 pm
Ed Wagner wrote:Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing." The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is. It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
I had hopes that the GDPR would actually start to move the needle on this stuff, but I don't think it's going to. It's pretty clear that businesses are going to undermine all the laws and take the teeth out of them so that we can carry with business as horribly usual.
"The credit belongs to the man who is actually in the arena, whose face is marred by dust and sweat and blood"
- Theodore RooseveltAuthor of:
SQL Server Execution Plans
SQL Server Query Performance Tuning -
May 24, 2019 at 5:51 pm
Ed Wagner wrote:Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing." The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is. It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
I'll also say that we dumb down early examples, POCs, and frameworks too much early on. We provide (and many of us as speakers are to blame), poor practices that people try to build on. I can't quite decide how to make better examples, but I have started to try and ensure I always show stupid long passwords, don't use dynamic SQL in an app view, etc. Give someone more secure copy-pastable code.
-
May 24, 2019 at 5:53 pm
Grant Fritchey wrote:I had hopes that the GDPR would actually start to move the needle on this stuff, but I don't think it's going to. It's pretty clear that businesses are going to undermine all the laws and take the teeth out of them so that we can carry with business as horribly usual.
I think it is, but slowly, and not consistently. Bigger companies keep finding ways around them, but smaller companies are doing a better job in many cases. I've been surprised how much better some of the data catalog stuff has taken off, and there do seem to be better new code. The hard part is little value in changing old code unless you get hacked.
Most managers (even some devs) would rather roll the dice and leave old code alone
-
May 27, 2019 at 7:00 pm
Ed Wagner wrote:Grant Fritchey wrote:I just presented a new session on SQL Injection at Techorama in Belgium and before that at SQLDay in Poland. As part of the prep, I did searches on recent breaches caused by Injection. There are so many. It's completely disheartening. The Georgia Tech one was bad. A worse one was iDressUp, a kids site. It's just nuts that we're dealing with this crap after 21 years of knowing how to fix it.
Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing." The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is. It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
Have you guys looked at the "SQL Injection Hall of Shame"? http://codecurmudgeon.com/wp/sql-injection-hall-of-shame/
Wayne
Microsoft Certified Master: SQL Server 2008
Author - SQL Server T-SQL Recipes
If you can't explain to another person how the code that you're copying from the internet works, then DON'T USE IT on a production system! After all, you will be the one supporting it!
Links:
For better assistance in answering your questions
Performance Problems
Common date/time routines
Understanding and Using APPLY Part 1 & Part 2 -
May 28, 2019 at 11:03 am
WayneS wrote:Have you guys looked at the "SQL Injection Hall of Shame"? http://codecurmudgeon.com/wp/sql-injection-hall-of-shame/
Oh yeah. It's part of my presentation.
"The credit belongs to the man who is actually in the arena, whose face is marred by dust and sweat and blood"
- Theodore RooseveltAuthor of:
SQL Server Execution Plans
SQL Server Query Performance Tuning -
May 28, 2019 at 11:22 am
WayneS wrote:Ed Wagner wrote:Grant Fritchey wrote:I just presented a new session on SQL Injection at Techorama in Belgium and before that at SQLDay in Poland. As part of the prep, I did searches on recent breaches caused by Injection. There are so many. It's completely disheartening. The Georgia Tech one was bad. A worse one was iDressUp, a kids site. It's just nuts that we're dealing with this crap after 21 years of knowing how to fix it.
Yes, it's insane that it isn't taken more seriously. People will say that they take it seriously, but then not give the people what they need to do it correctly. They hire people who don't know, don't train them, impose unrealistic deadlines and then complain about how much stuff costs. It all starts with the education people don't receive and that feeds the hiring. Like Jeff says, "They know the cost of everything and the value of nothing." The managers are also the ones to have CYAs and DKs lined up, cover things up for months after a breach occurs and then release as little detail as possible to the public. Just look how bad the the USPS or Equifax ones were. I have a presentation that has a "slide of shame" with some of the larger hacks and it's sad just how busy it is. It's way past time for companies to take security seriously. The attitude of management and bad development practices have gotten the IT industry to where it is today.
Have you guys looked at the "SQL Injection Hall of Shame"? http://codecurmudgeon.com/wp/sql-injection-hall-of-shame/
I didn't know about that one. Thank you, Wayne. It'll be included in future versions of that presentation.
-
May 28, 2019 at 1:12 pm
I just can't believe some people. I requested our DBA to gather statistics from sys.dm_exec_procedure_stats in production and store them in a non-production database for analysis without compromising permissions.
Yesterday he emailed to notify that the process had been implemented. Today, when I'm looking for the table and can't find it, I ask him for it. He just created it on production and offered to copy it whenever I need it. I ASKED FOR THE TABLE TO AVOID HAVING TO REQUEST IT EVERY SINGLE TIME!
I'm really not sure how I should reply to him.
Viewing 15 posts - 63,616 through 63,630 (of 66,905 total)
You must be logged in to reply to this topic. Login to reply