Introduction
You may want to provide access to the files from your Azure storage account container, there are a couple of ways to do it. You can share the access key but it may not be the best option because this is something you want to keep secret. Azure Active Directory Authentication is another option but it may not be available always to the client. In this article, we will discuss providing limited access to the Azure storage accounts resources by using shared access signatures (SAS) and Access Policy.
Shared Access Signature
A shared access signature (SAS) provides a URI that grants restricted access rights to Azure Storage resources. With SAS, you have granular control over how a client can access your data. By distributing a shared access signature URI to these clients, you grant them access to a resource for a specified period of time. For example:
- What services the client may access.
- What permissions they have to those resources.
- How long the SAS is valid.
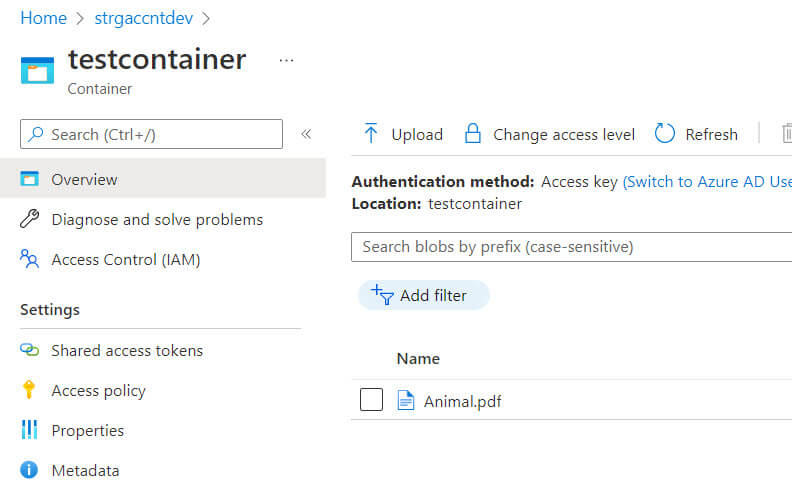
Let's assume that we want to share the below file Animal.pdf from the azure storage container:
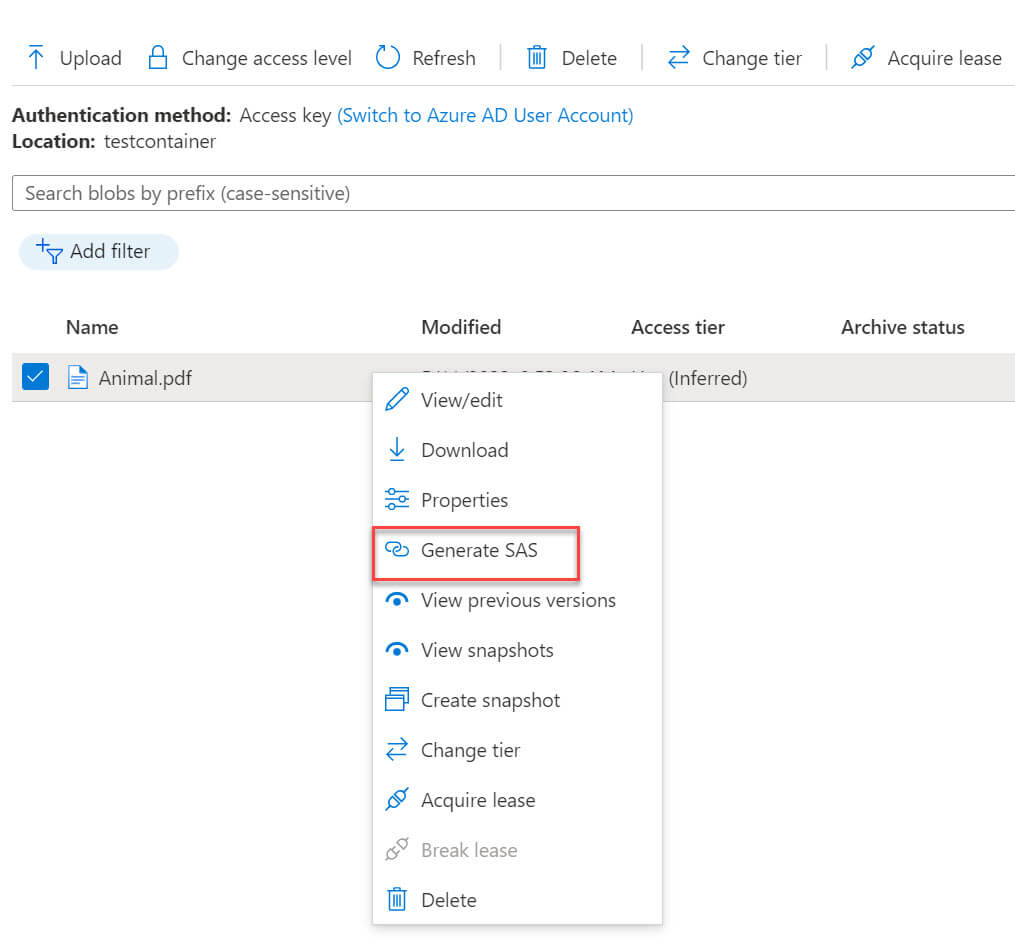
Right-click on the file and select generate SAS option:
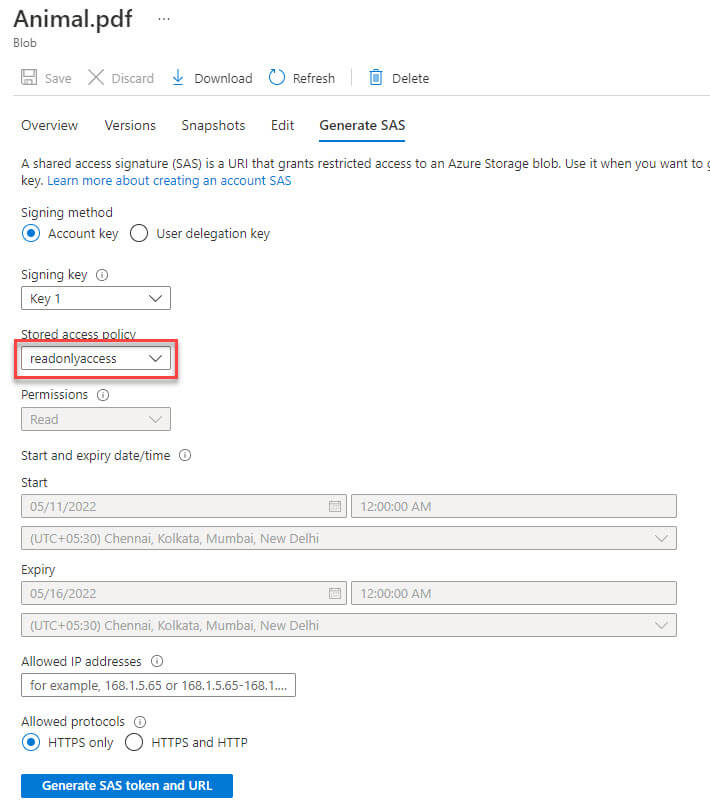
Now, we need to provide the below details to create the SAS:
- Signing method - Choose between Account Key and User Delegation key. You must create a user delegation key then you can use it to create the SAS.
- Signing key - Select between Key 1 and Key 2.
- Stored access policy - Select None.
- Permissions - Select from available options Read,Add,Create,Write,Delete,Permanent Delete,Tags and Immutable storage.
- Start and expiry date/time - Start and expiry date/time during which the SAS is valid.
- Allowed IP addresses - Optionally, you can choose IP address or IP address range.
- Allowed protocols - HTTPS only or HTTPS and HTTP. It is recommended to use HTTPS.
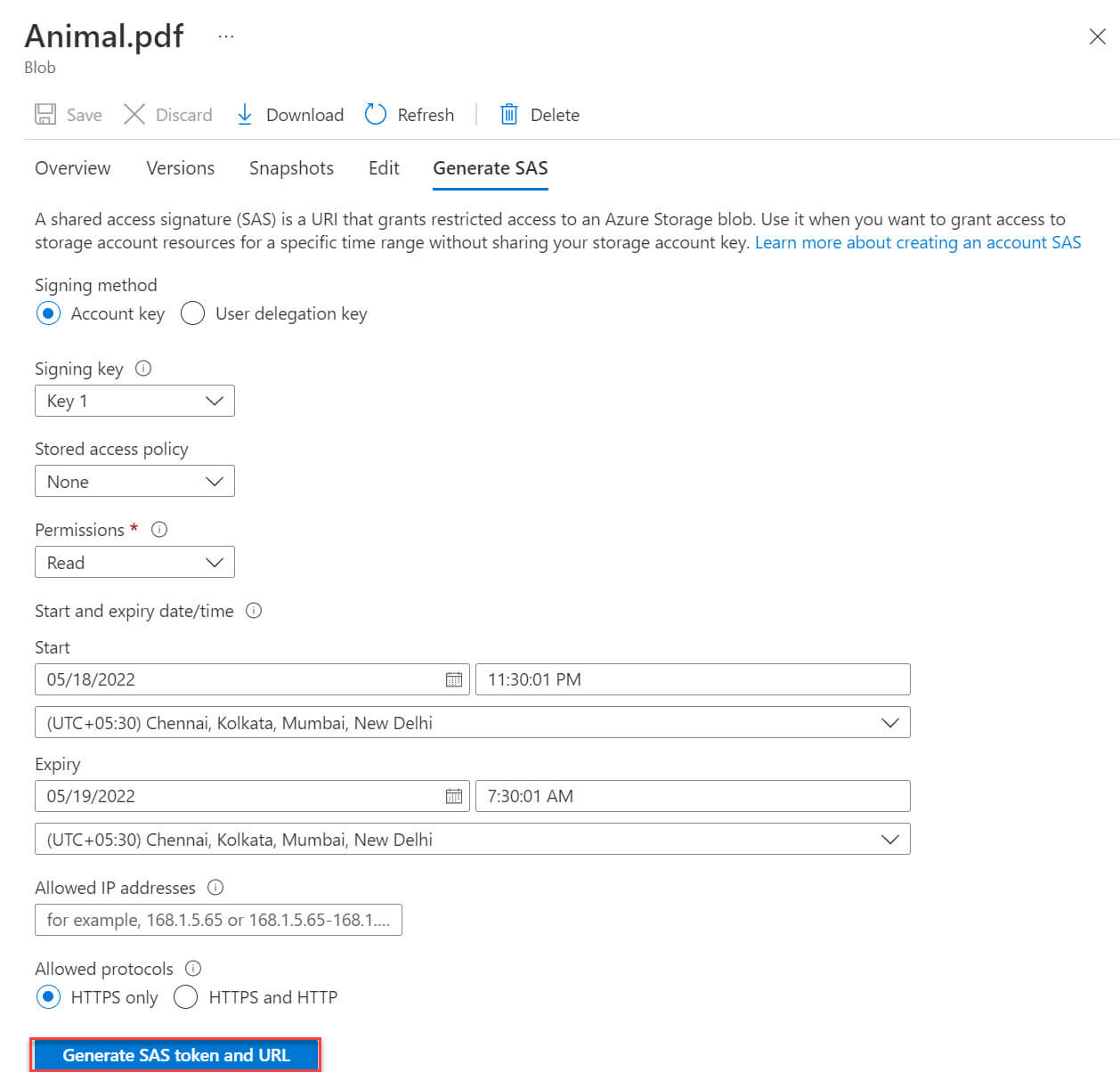
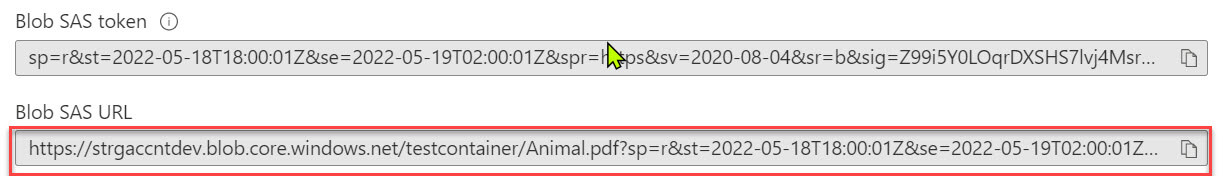
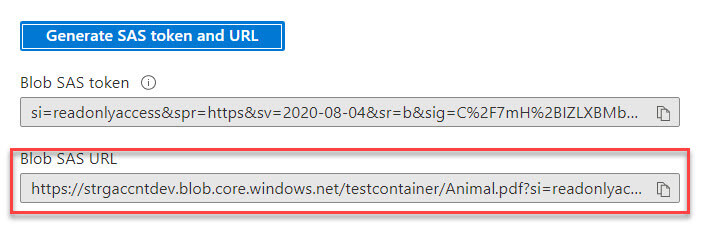
Now the blob SAS token and blob SAS URL are created:
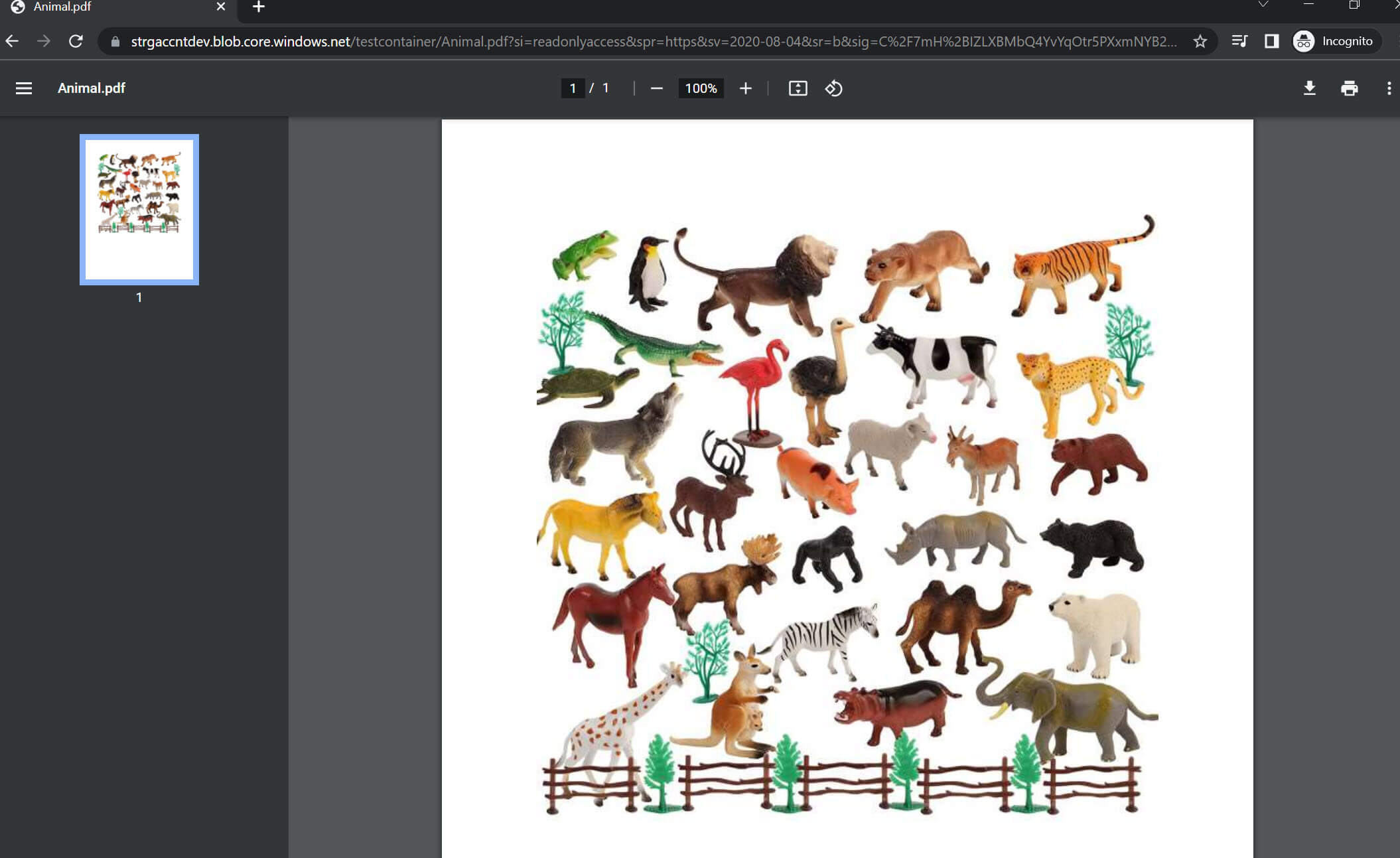
We can access the file from the browser:
We can use the blob service SAS URL to access storage account resources. But there is a drawback to the shared access signature, it does not track the number of shared access signatures that have been generated for a storage account, and no API can provide this detail. You need to track manually if you want to keep details of the number of shared access signatures that have been generated for the account.
Access policy
We can create an Access policy in the storage account container to provide an additional layer of security in the resources. The Access policy is available under the settings option. Click on Add policy inside the Stored Access Policy section :
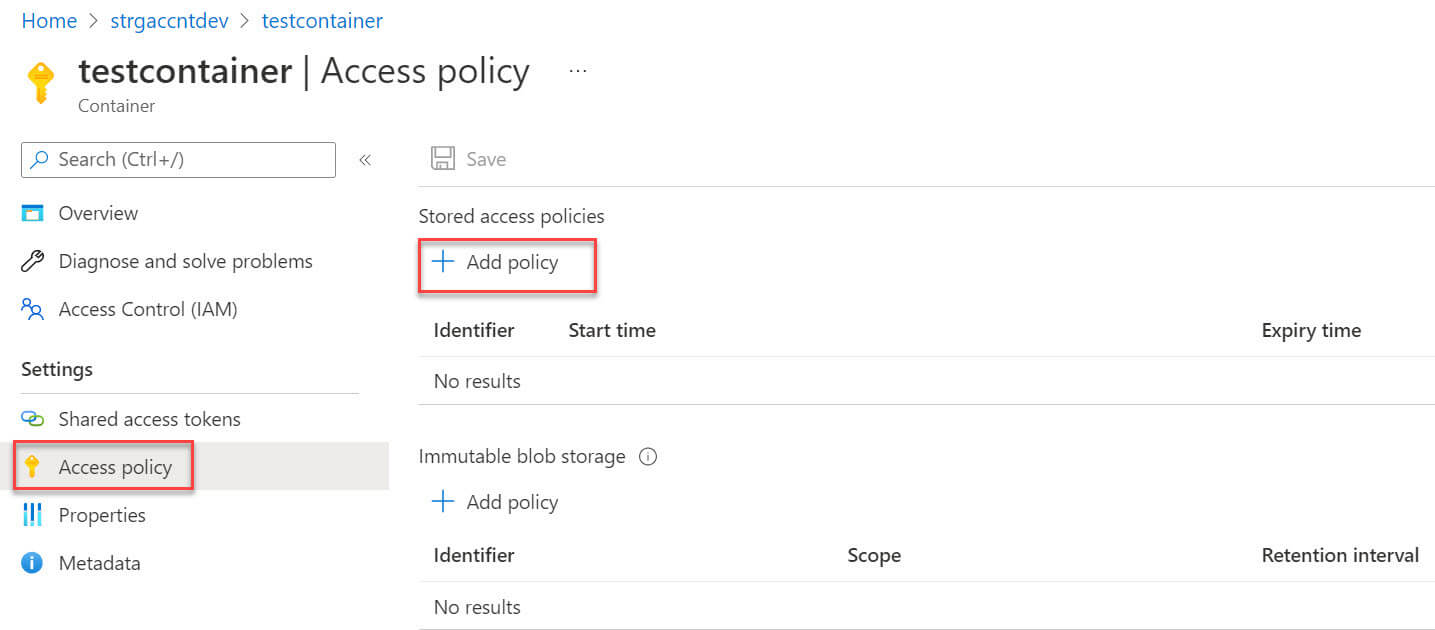
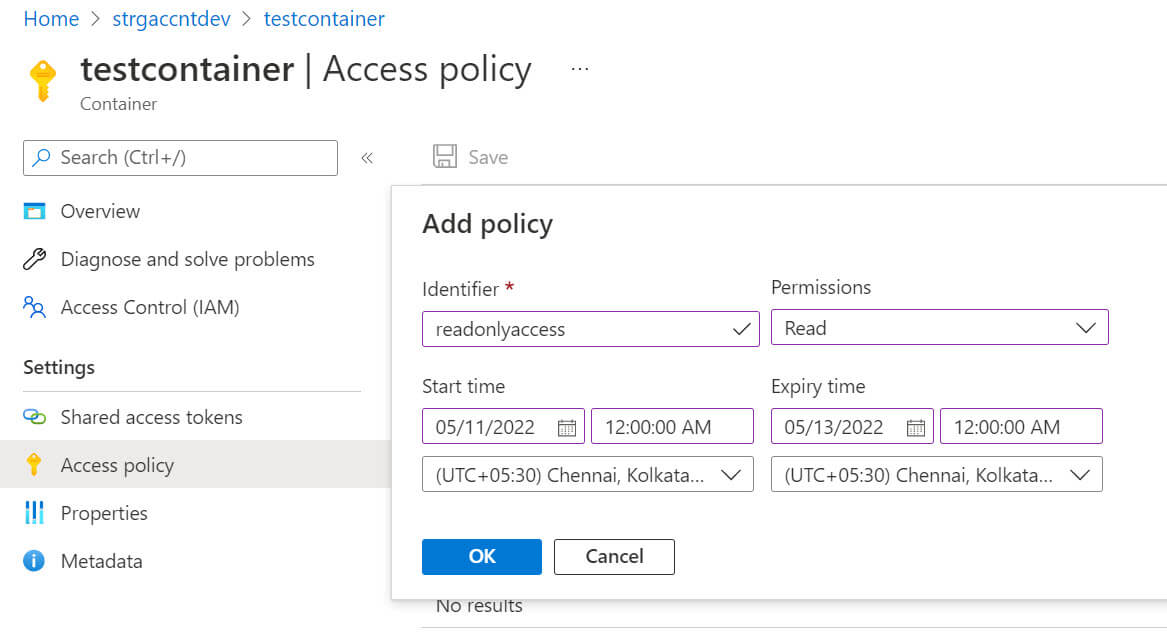
We need to provide the below details to create a policy:
- Identifier - Provide a name to this policy.
- Permissions - Select permissions from the list, available options are Read, Add, Create, Write, Delete and List
- Start time - Access Policy start time.
- Expiry time - Access Policy end time.
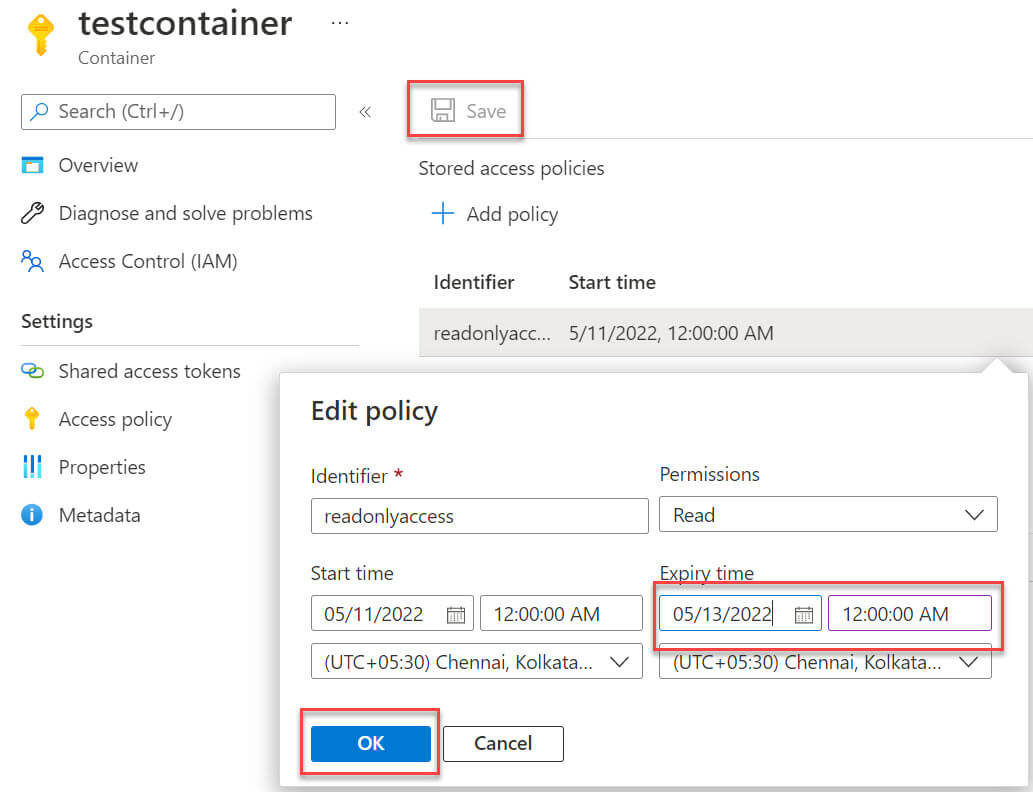
Click OK and then click on Save to create this policy:
Let's create the SAS again with an access policy.
Click on the file Animal.pdf file menu option:
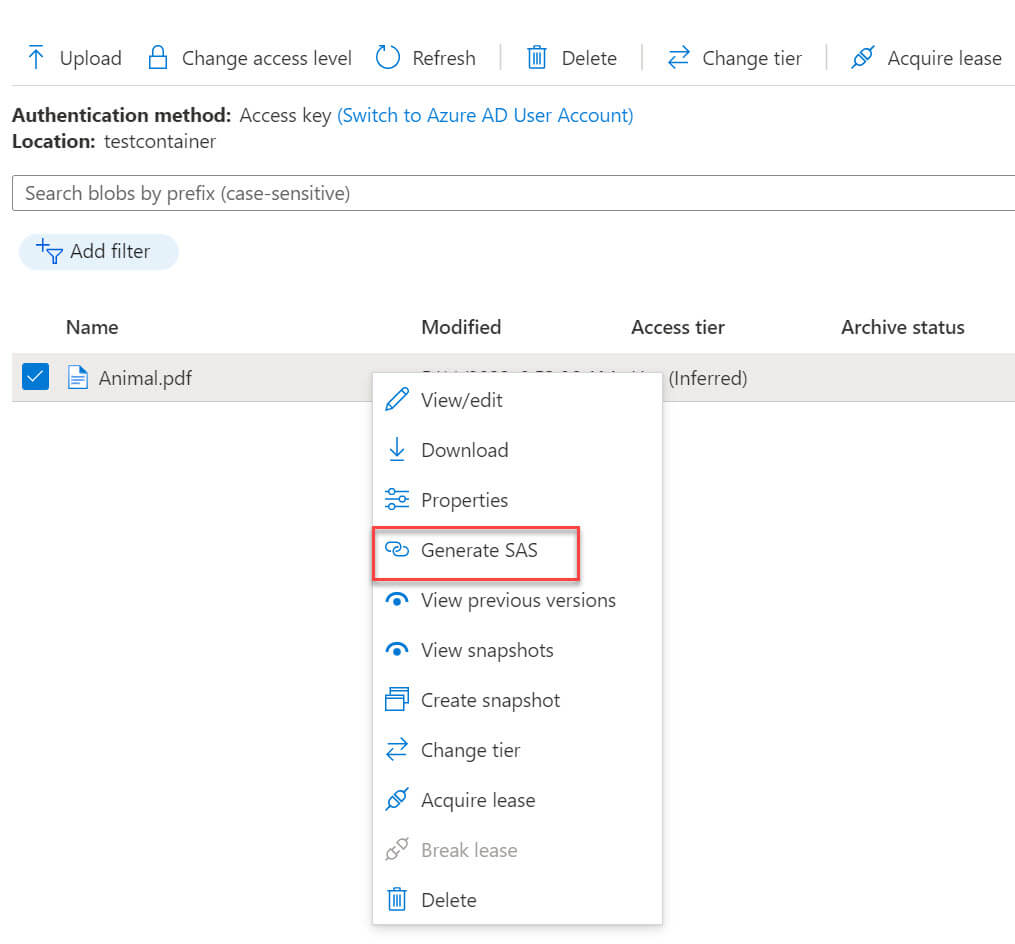
Now in the stored access policy option, select the access policy readonlyaccess which we created earlier, note that other options permissions, start, and expiry date/time are not editable now because these options will be inherited from stored access policy:
The blob SAS URL generated:
I copied the URL and pasted it to the browser. The file can be accessed now:
Now we want to revoke the access to the shared file, to do that we can edit the access policy :
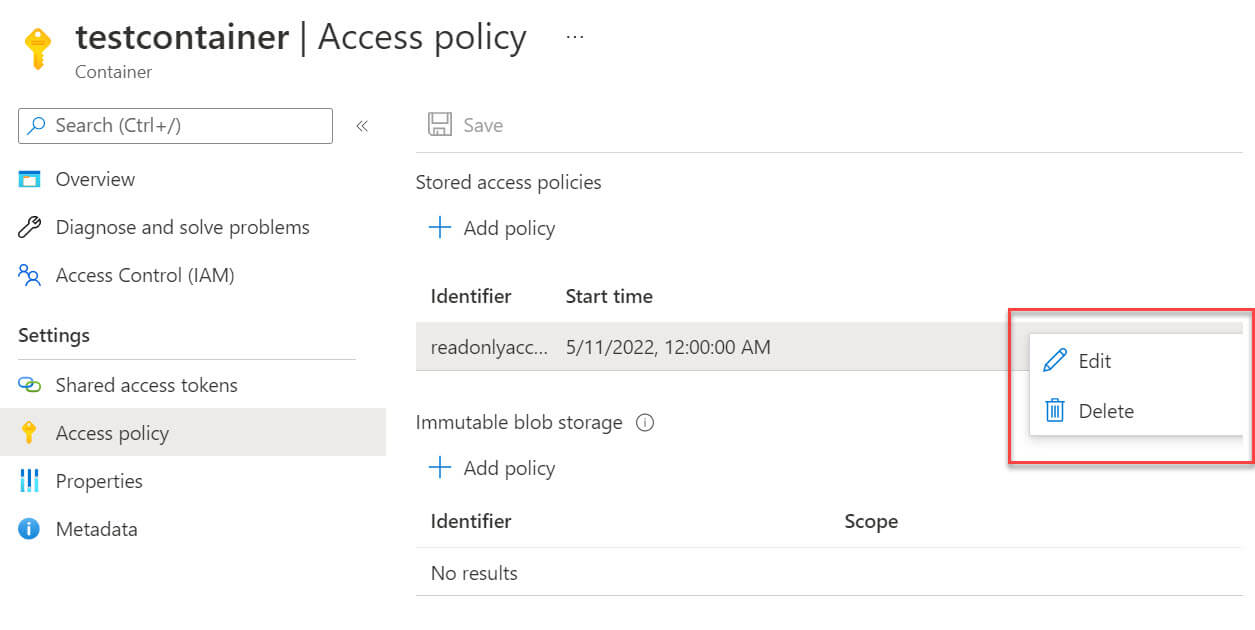
We can put an old date in the expiry time to end this access policy :
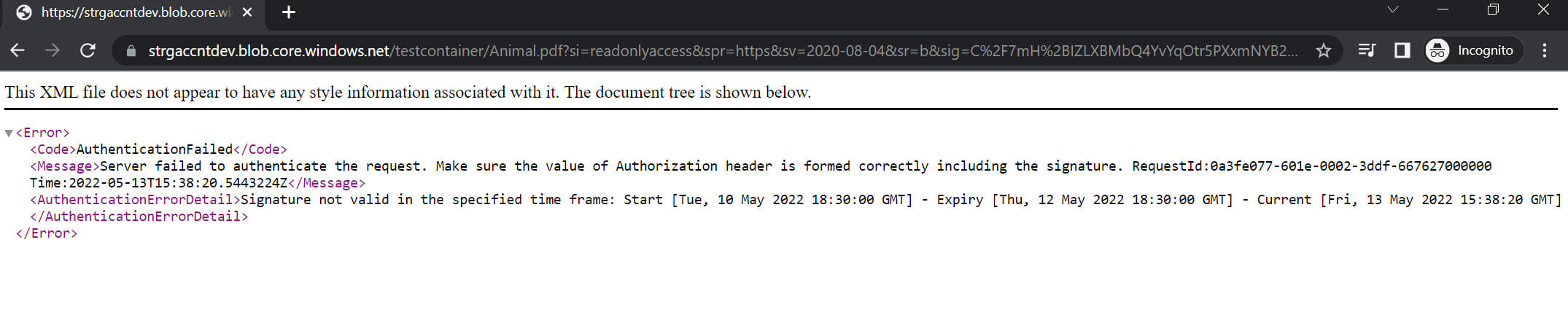
Let's try to access the file again and as expected the file is not accessible now :
Conclusion
A stored access policy provides additional control over the shared access signature. You can easily manage a stored access policy to change the start time, expiry time, or permissions for a signature or revoke it after it has been issued.

