Using Active Directory groups are a great way to manage and maintain security for a solution. Think about if you had to manually add users to your Analysis Services roles each time someone new wanted access to your cube. Ideally, you would have an AD group in the SSAS role membership and anytime someone wants access to the cube they simply need to get added to the AD group and nothing would need to be changed in Analysis Services.
My goal in this post is not to convince you that AD groups are a good thing. Hopefully you already understand that. What I really want to show you is a few “tricks” for dealing checking permission to AD groups.
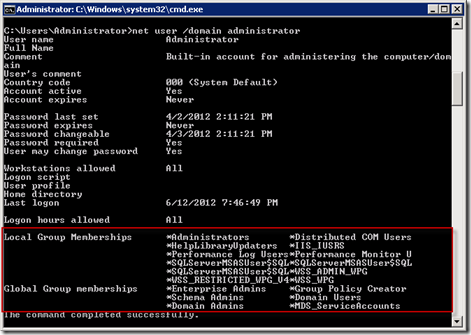
The first example will return back all AD groups that a user is a member of and lots of other good information about a selected user. When troubleshooting access to your solution this gives you a quick way to rule out membership to the proper AD group as a possible issue.
Open a command line prompt by clicking your Start Menu and then select Run. Type CMD and click OK where you will use the following code:
Template:
net user /domain “<AD Account>”
Example:
net user /domain “dknight”
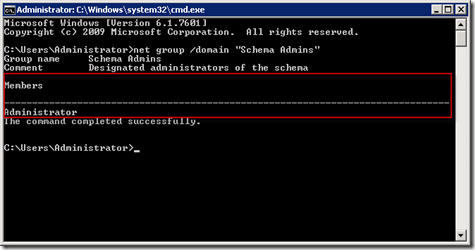
The second example will return all users that are members of a specified AD group. Open a command line prompt again and use the following code:
Template:
net group /domain “<AD Group>”
Example:
net group /domain “Schema Admins”
While these seem like simple commands you may find them very useful when troubleshooting permission errors. Another great thing is you don’t have to be a server admin to use these just about anyone can run them.