Following up from last week’s post on Azure Key Vault in this blog I will show you how to the setup Key Vault logging I mentioned for auditing access and usage of your key vault. Once we walk through the process of enabling your logging, we will configure Azure Log Analytics as a way to analyze that data. Azure Log Analytics uses advanced analytics and machine learning to analyze your azure log files. It adds intelligent insights to your monitored data such as Key Vault usage and access as well as latency in key retrieval from your Audit Event Logs.
Here is the PowerShell Script you can use to enable logging.
#If you have never used Powershell for Azure you will need to run the below line as Administrator #Install-Module -Name Az -AllowClobber #Connect to Your Azure Account (Will prompt you for your azure credentials into Azure) Connect-AzureRmAccount #Connect to Azure Subscriptions (To get a list of all your subscription ID's highlight the one you need for next step and copy and past below) Get-AzureRmSubscription #Specify Your Subscription You Want to Work With Set-AzureRmContext -SubscriptionId Your ID Here #Create Storage Account # If you need to create a storage account you can use this $sa = New-AzureRmStorageAccount -ResourceGroupName SQLDB-Development -Name dcackeyvaultstorage -Type Standard_LRS -Location 'East US 2' #Identify Your Key Vault $kv = Get-AzureRmKeyVault -VaultName 'DCACAEKeyVaultDemo' #Enable Logging (uses $kvand $sa parameter from above) Set-AzureRmDiagnosticSetting -ResourceId $kv.ResourceId -StorageAccountId $sa.Id -Enabled $true -Categories AuditEvent #Set Retention Period for Your Logs (uses $kvand $sa parameter from above) Set-AzureRmDiagnosticSetting -ResourceId $kv.ResourceId -StorageAccountId $sa.Id -RetentionEnabled $true -RetentionInDays 90
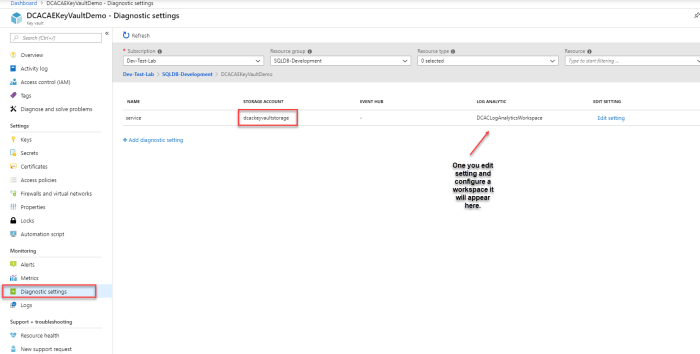
After logging is enabled these logs can then be easily analyze with Log Analytics. You’ll need to configure it like the below.
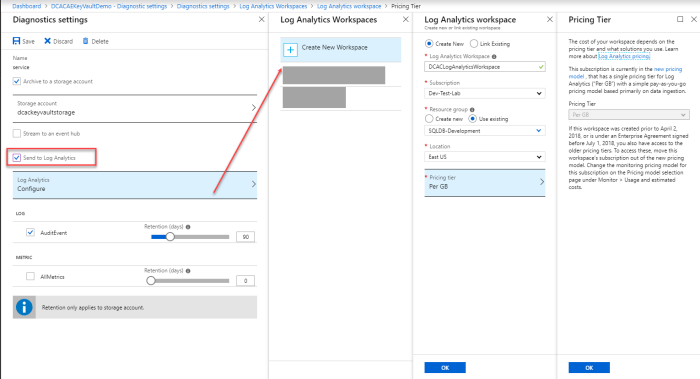
Under Diagnostic Setting Choose Edit
In this screen you will validate your storage account where the logs will be stored and your retention period that you setup using the above PowerShell scripts. The next step is to create a Log Analytics Workspace. Just click Create New Workspace and choose what subscription and resource group you want it located. Just like any other resource within Azure, you will need to choose your location and the pricing tier associated with it. You should note that the first 5 GB of log data per month is free, and there are reasonable costs beyond that. In this case it’s only choice for pricing is Per GB as you can see below. Then it ok and save.
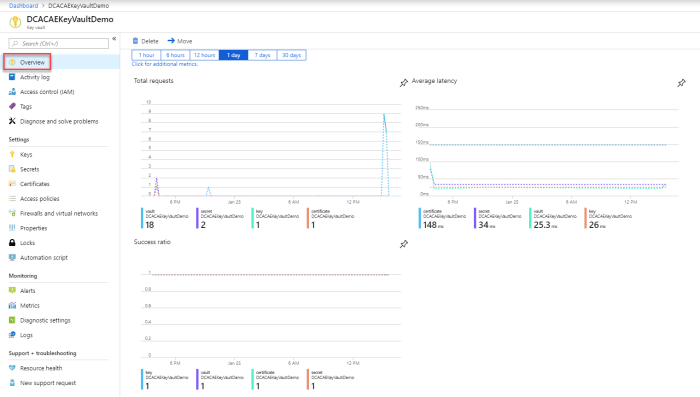
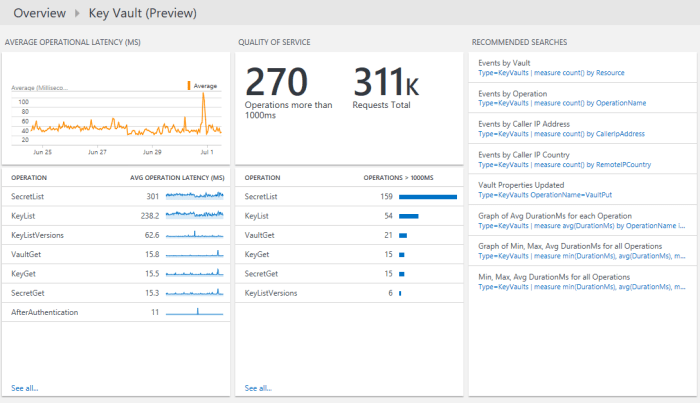
Within 10 minutes of setting up logging and Log Analytics you’ll be able to see your data. Logging will look like this under the Overview Section.
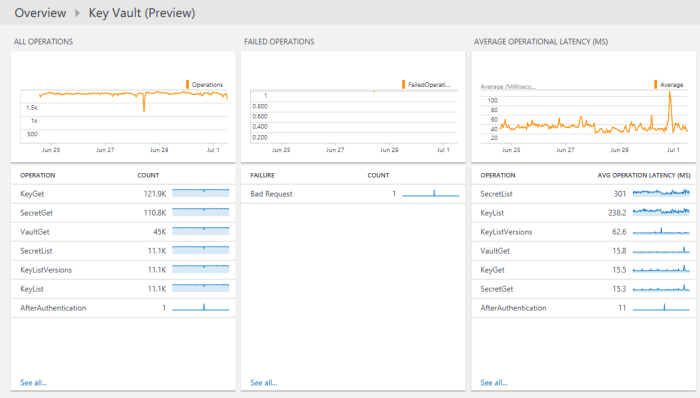
Per MSDN you can view summaries of your logs and then drill in to details for the following categories:
- Volume of all key vault operations over time
- Failed operation volumes over time
- Average operational latency by operation
- Quality of service for operations with the number of operations that take more than 1000 ms and a list of operations that take more than 1000 ms
Here is what it looks like to drill in. Since I am not really using my Key Vault in production these examples from MSDN better show what your results will be like.
As you can see it’s very easy to set up. If your company is like most, you will want to set up a way to report on Key Vault usage Azure Log Analytics gives you everything you may want. You’ll find costs are minimal and it’s a great an essential piece of your entire key management process.